 |
MPHELL
5.0.0
|
 |
MPHELL
5.0.0
|
Define an EdDSA signature. More...
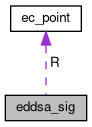
Data Fields | |
| ec_point | R |
| number * | s |
Define an EdDSA signature.
Some documents to get more informations about EdDSA standard and hash standard functions. We mainly follow [EdDSA15] [FIPS-180] FIPS 180-4: Secure Hash Standard by the National Institute of Standards and Technology, august 2015, (March 2019) http://dx.doi.org/10.6028/NIST.FIPS.180-4
[FIPS-186] FIPS 186-5: Digital Signature Standard by the National Institute of Standards and Technology, october 2019, (April 2021) https://csrc.nist.gov/publications/detail/fips/186/5/draft
[FIPS-202] FIPS 202: SHA 3 Standard: Permutation based hash and extendable output functions by the National Institute of Standards and Technology, august 2015, (March 2019) http://dx.doi.org/10.6028/NIST.FIPS.202 [SP-800] SP 800-107 Recommendation for application using approved hash algorithms by Quynh Dang of the National Institute of Standards and Technology, august 2012, (March 2019) https://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication800-107r1.pdf Ed448-Goldilocks, a new elliptic curve by Mike Hamburg (May 2021) https://eprint.iacr.org/2015/625.pdfs [rfc 8032] Edwards-Curve Digital Signature Algorithm (May 2021) https://tools.ietf.org/html/rfc8032
Some documents to get more informations about EdDSA standard and hash standard functions. We mainly follow [EdDSA15] [EdDSA15] EdDSA for more curves by Daniel J Bernstein, Simon Josefsson, Tanja Lange, Peter Schwabe, Bo-Yin Yang, july 2015, (March 2019) https://ed25519.cr.yp.to/ed25519-20110926.pdf [FIPS-180] FIPS 180-4: Secure Hash Standard by the National Institute of Standards and Technology, august 2015, (March 2019) http://dx.doi.org/10.6028/NIST.FIPS.180-4
[FIPS-186] FIPS 186-4: Digital Signature Standard by the National Institute of Standards and Technology, july 2013, (March 2019) http://dx.doi.org/10.6028/NIST.FIPS.186-4
[FIPS-202] FIPS 202: SHA 3 Standard: Permutation based hash and extendable output functions by the National Institute of Standards and Technology, august 2015, (March 2019) http://dx.doi.org/10.6028/NIST.FIPS.202 [SP-800] SP 800-107 Recommendation for application using approved hash algorithms by Quynh Dang of the National Institute of Standards and Technology, august 2012, (March 2019) https://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication800-107r1.pdf
Definition at line 55 of file mphell_tuto_eddsa-448+25519.c.
| ec_point R |
First signature point, belongs to the signature curve
Definition at line 57 of file mphell_tuto_eddsa-448+25519.c.
| number * s |
Second signature number, belongs to [1, n-1]
Definition at line 58 of file mphell_tuto_eddsa-448+25519.c.