 |
MPHELL
5.0.0
|
 |
MPHELL
5.0.0
|
The MPHELL library implements Elliptic Curve arithmetic:
We provide a Simple Power Analysis (SPA) resistant multiplication using unified addition (and COZ arithmetic for Weierstrass curves).
Some dedicated addition / doubling are also provided to improve performances when security is not required.
Available curve types:
Possible conversion:
Available coordinates for Weierstrass elliptic curve:
Available coordinates for Twisted Edwards elliptic curve:
Available coordinates for extended Jacobi Quartic elliptic curve:
Curve can be given manually giving
Some known curves are hardcoded and can be setup by their names (eg: FR_256, BRAINPOOL_512, NIST_521, ...).
This library can be used on Linux operating system (x86, 32 and 64 bits), on ARM 32 bits (tested on Raspberry Pi 2) and on microcontroller (tested on STM32F4).
The modular (field level) arithmetic is either managed by
The Adapted Modular Number System (AMNS) code uses strongly the thesis of Fangan-Yssouf Dosso: Contribution de l’arithmétique des ordinateurs aux implémentations résistantes aux attaques par canaux auxiliaires, 2020. And the paper: Efficient modular operations using the adapted modular number system. Journal of Cryptographic Engineering, Springer, 2020. from Pascal Véron. Laurent-Stéphane Didier, Fangan-Yssouf Dosso. The AMNS is especially well fitting for current elliptic curve prime size on 64 bits target when 128 bits integer are available. In this case we set up AMNS as default. When AMNS is used, GMP is still needed for conversion from classical form to AMNS but no arithmetic operation is done using GMP. Some AMNS have been hardcoded for some known elliptic curves, but often many AMNS can be use for a same prime field. The AMNS format used by MPHELL is the one given by the AMNS generator provided here AMNS Generator. MPHELL is able to parse the resulting string from this generator to use the given AMNS. AMNS become less efficient for curve with prime field size higher than 384 bits. If you mainly use curve of 512 bits or more, it can be interresting to disable AMNS.
GMP (without AMNS), is generic and gives for instance the best compromise on a raspberry PI 4 (ARM 64 bits)
IPP can be faster for some NIST curves, but for x86 only.
MbedTLS is interresting on stm32 microcontroller (dedicated ASM), but suprinsingly AMNS gives also good performances on this target. MbedTLS version must be higher than 2.11 and stricly lower than 3.0 (version 3 change of API).
When GMP or MbedTLS is used for the big number arithmetic, the field arithmetic is then build over this big number arithmetic. We can choose (at configure time) to use either a
Available finite fields are
MPHELL has a random number generation system in accordance with the "NIST Special Publication 800-90A".
The seed (and the nonce) are extrated from one of the entropy source available in MPHELL:
Two types of DRBG are supported in MPHELL:
If –enable-vectorization=yes then MPHELL uses the AES NI instructions set.
The following parameters are used by MPHELL when using its own DRBG:
Two types of Random Generator using their own entropy source are available in MPHELL:
The 15 tests made by the the NIST sts program, have been passed by all the combination of MPHELL entropy and DRBG availables. In order to fullfill the requirements of all the tests we used the following parameters:
The DRBG (both HASH-DRBG and CTR-DRBG) are tested with the NIST vector tests while running "make check"
In order to avoid multiple system calls (malloc, free, ...) we use some temporary memory stacks and some pools of already initialised field elements.
BEWARE: Element on the stack should be free in the reverse order than their allocation:
In order to use MPHELL in different threads you must:
If you got MPHELL from the git repository run (require autoconf, automake, libtool): autoreconf --i
We advide to create a directory: mkdir obj_dir && cd obj_dir
then run configure from there using ../configure instead of ./configure
Run the classical commands:
If GMP is install in /path/to/gmp, run the commands:
If ipp-crypto is install in /path/to/ipp-crypto (ex: /home/softs/ipp-crypto), run the commands:
Run the classical commands:
If GMP is install in /path/to/gmp, run the commands:
MbedTLS version must be higher than 2.11 and stricly lower than 3.0 (version 3 change of API).
Run the classical commands:
If MbedTLS is install in /path/to/mbedtls, run the commands:
Default values are in uppercase.
A toolchain for bare metal compilation is available here: arm-none-eabi toolchain
You can add the path of your toolchain binaries to the PATH environnement variable with: export PATH=$PATH:/path/to/toolchain/bin
Despite the not optimize 32 bits AMNS for ECC field size, it gives some goop performances on STM32F4
MbedTLS provides a fast arithmetic on the NIST curves for the STM32F4 compare to GMP. However the good performances of AMNS on STM32F4 are now better on all the curves. However AMNS uses quite some memory space, and MbedTLS can be better on this point.
The sources of MbedTLS can be included in your project Makefile, and be crosscompiled with your project. These sources are in the repository Middlewares/Third_Party/ if you activated "mbedTLS" in the STM32CubeMX code generator.
On the same scheme than MbedTLS, you can add the sources of MPHELL to your project Makefile and crosscompile it with your project. We provide here a source directory with MPHELL configured for MbedTLS to paste in your Middlewares/Third_Party/ directory.
Jacobi Quartic elliptic curves
Conversion between Weiestrass and Jacobi Quartic elliptic curves
Conversion between Short Weierstrass Curve Model and Twisted Edwards Curves Model
All tutorial can be compile with gcc mphell_tuto_fp.c \
-I/your-gmp-location/include \
-L/your-gmp-location/lib \
-lgmp \
-I/your-mphell-location/include \
-L/your-mphell-location/lib \
-Wl,-rpath=your-mphell-location/lib \
-lmphell \
-o tuto_fp
by replacing mphell_tuto_fp.c and tuto_fp by the tutorial you want to compile.
Look at mphell_tuto_fp.c
MPHELL handle only quadratic field extension over FP, with irreducible polynomial x^2-a where a is a non square in FP
Look at mphell_tuto_fp2.c
MPHELL handle only cubic field extension over FP, with irreducible polynomial x^3-a where a is a non cubic element in FP
Look at mphell_tuto_fp3.c
One time MPHELL is instantiated, MPHELL provides functions to get random elements, at
The following tutorials are only to understand, and evaluate the underlying random process
Look at mphell_tuto_drbg.c
Look at mphell_tuto_random.c
Look at mphell_tuto_weierstrass.c
Look at mphell_tuto_jacobi_quartic.c
Look at mphell_tuto_edwards.c
Look at mphell_tuto_ecdsa.c or
Add -fopenmp to the compilation line (the signature verification is parallelised), verify that MPHELL was configure with "--enable-multithreading=yes" and
Look at mphell_tuto_ecdsa_fips.c
In case of problem using MPHELL, thanks to:
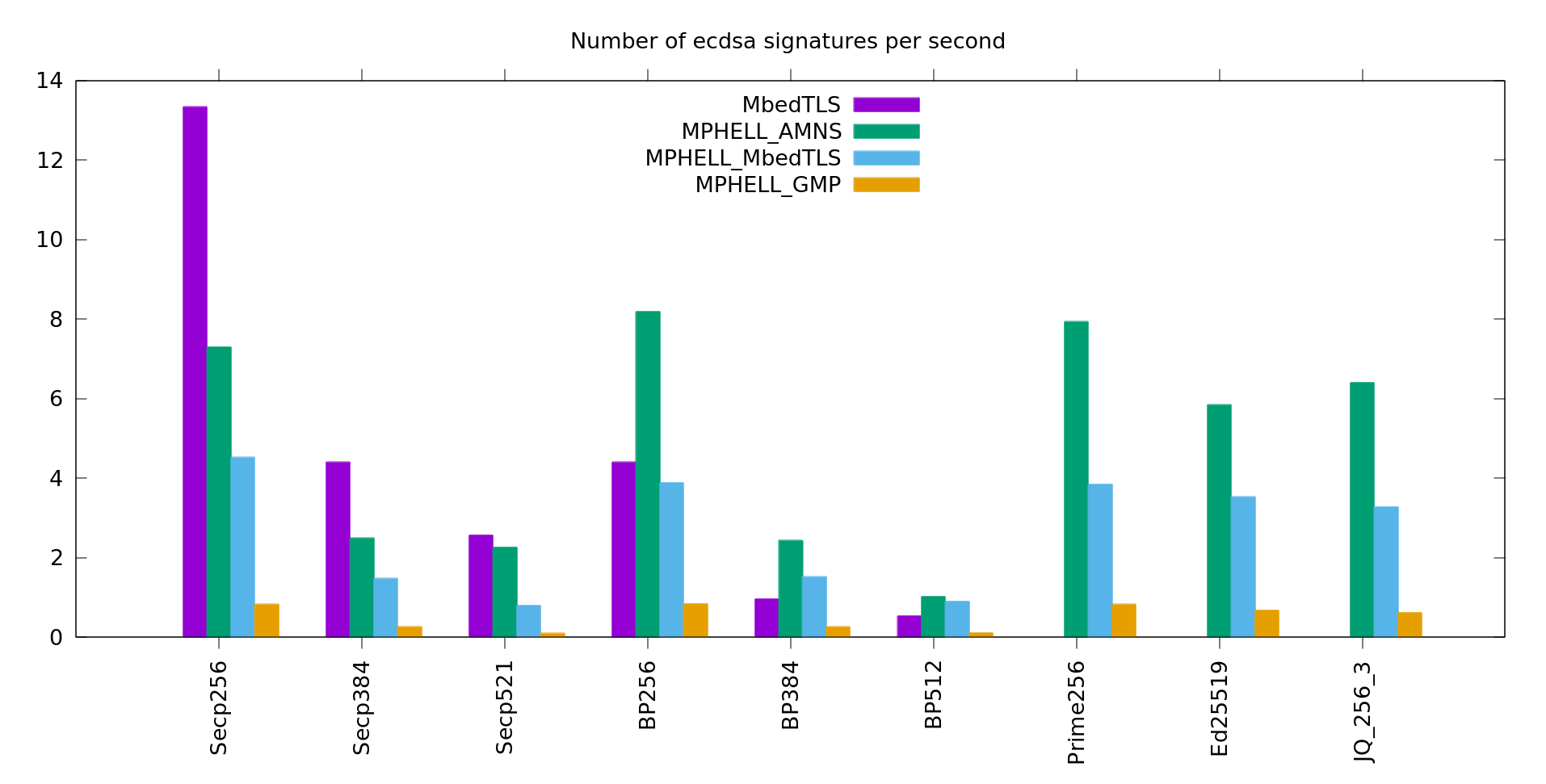
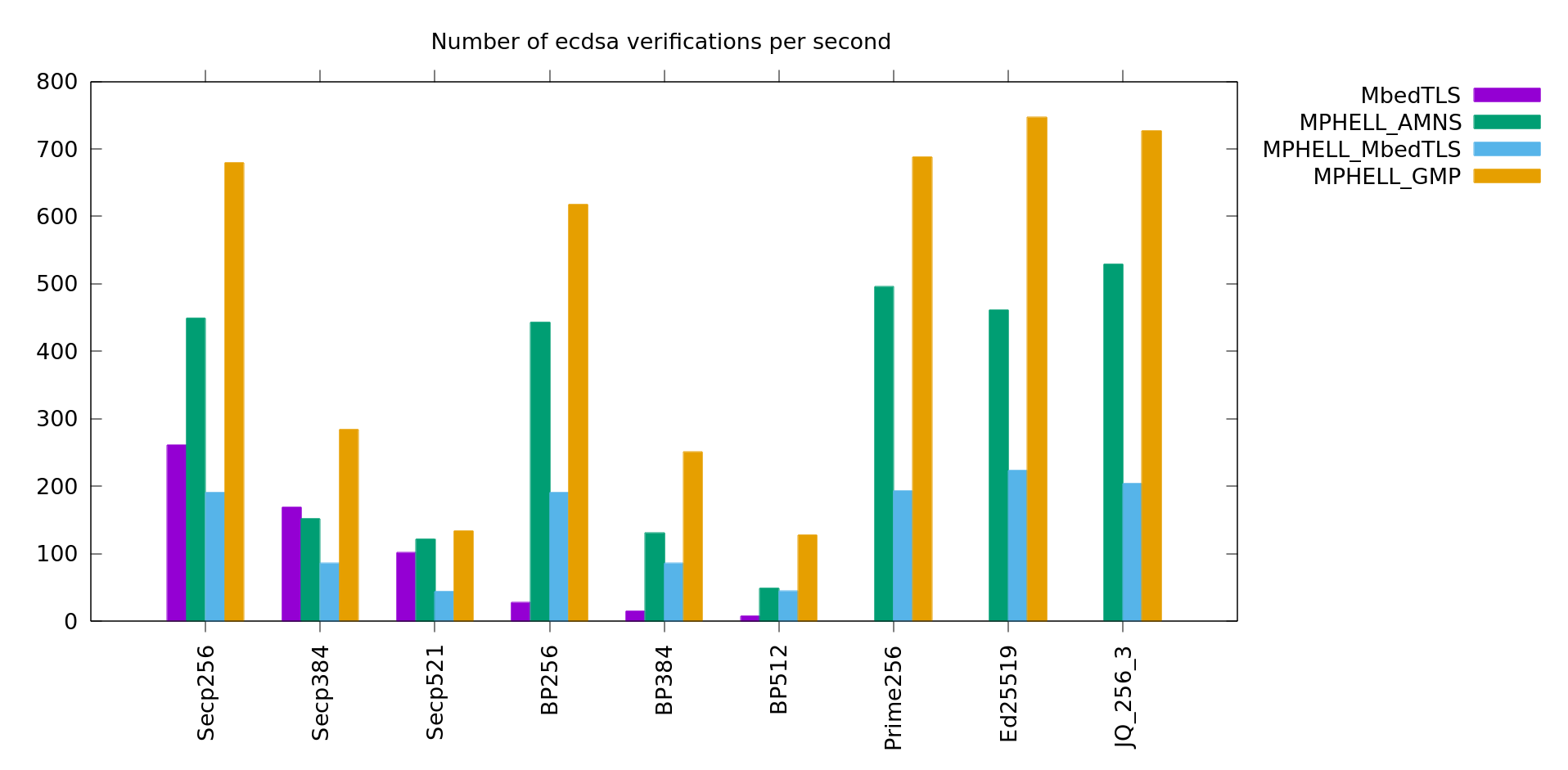
The benchmarks are made on a x86_64 architecture with an Intel Core i7-4790 CPU 3.60GHz × 8.
MPHELL uses some unified operations (slower) for the signatures to make it resistant to SPA, it's not the case for the others.
MPHELL uses some dedicated operations and some precomputation technics for the verification to make it faster.
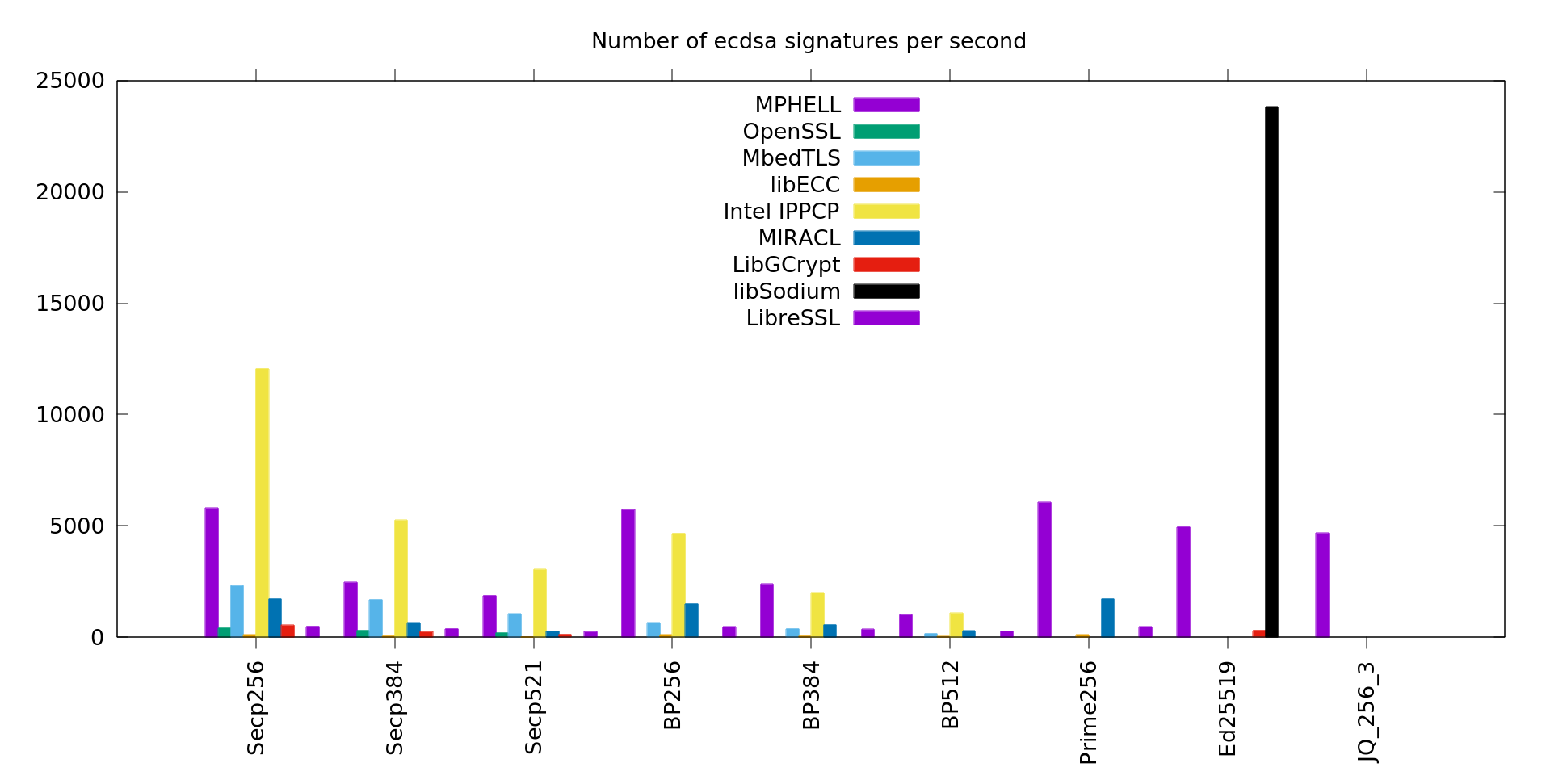
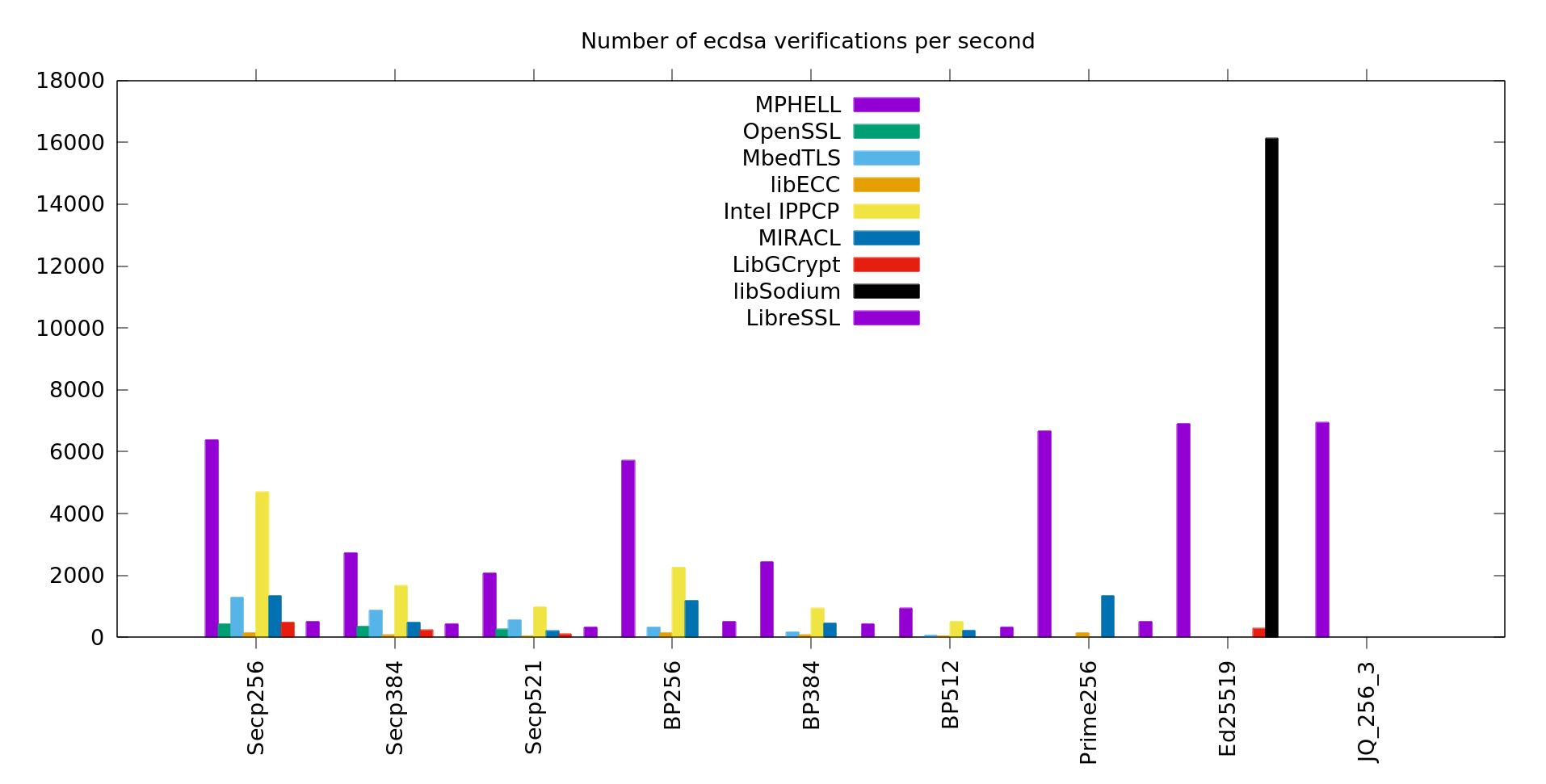
MbedTLS is faster for the signature because MPHELL uses a SPA resistant scalar multiplication (and not a windows one). Moreover MbedTLS has a dedicated arithmetic for the nist curves which is not implemented in MPHELL (except the NIST 521 which got a specially good AMNS).

MPHELL is faster for the verification because here the security against SPA is not required and we use an efficient sliding windows scalar multiplication. AMNS is efficient on STM32F4 despite the 32 bits restriction.
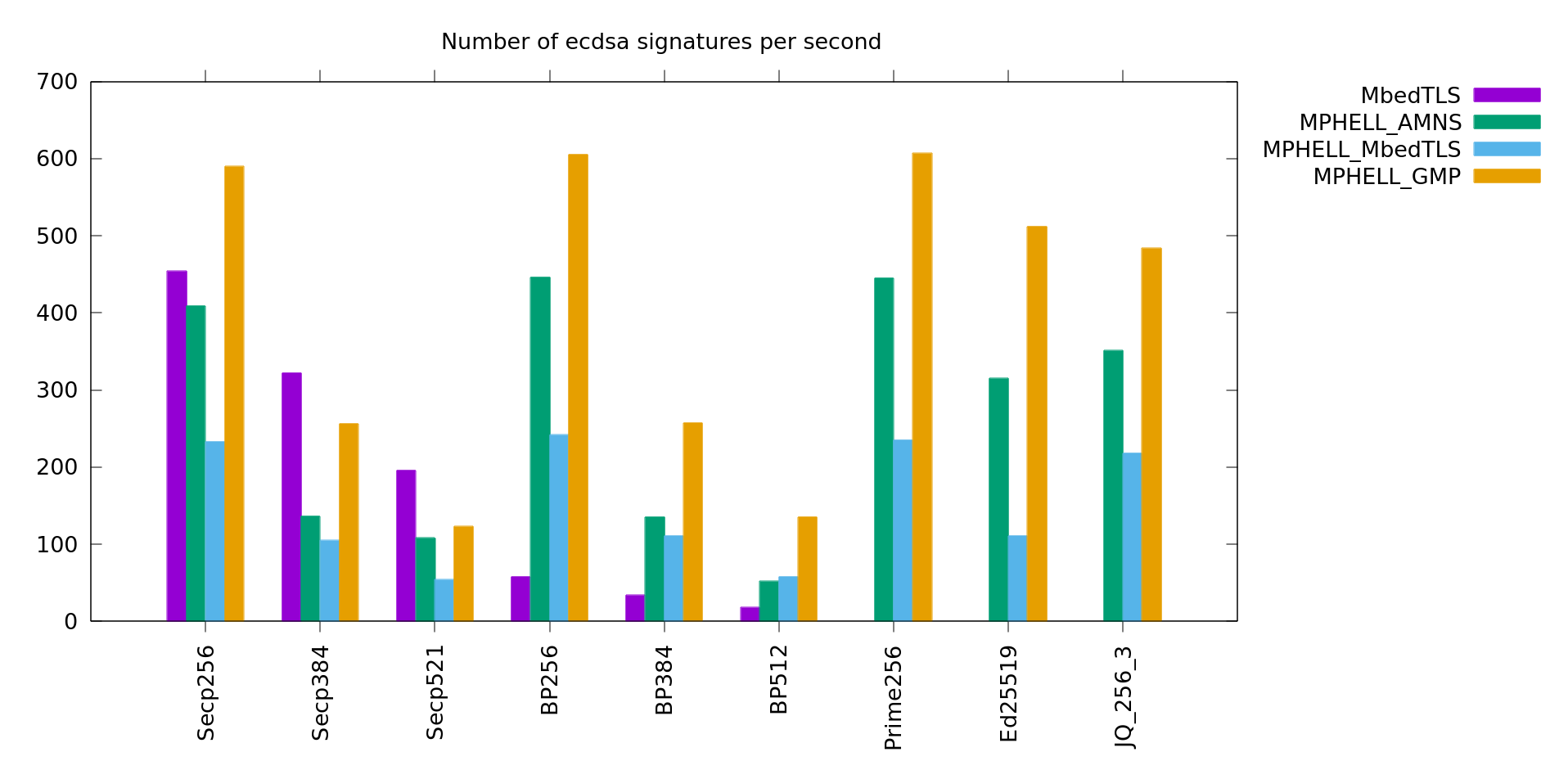
MbedTLS is sometimes faster for the signature because MPHELL uses a SPA resistant scalar multiplication (and not a windows one). Moreover MbedTLS has a dedicated arithmetic for the nist curves which is not implemented in MPHELL. AMNS cannot use 128 bits integers here and is slow.
MPHELL is faster for the verification because here the security against SPA is not required and we use an efficient sliding windows scalar multiplication.